2025 et=”_blank” href=”https://theguter.com/?p=8958″>et=”_blank” href=”https://theguter.com/?p=10083″>Cross-Chain Bridge Security Audit Guide
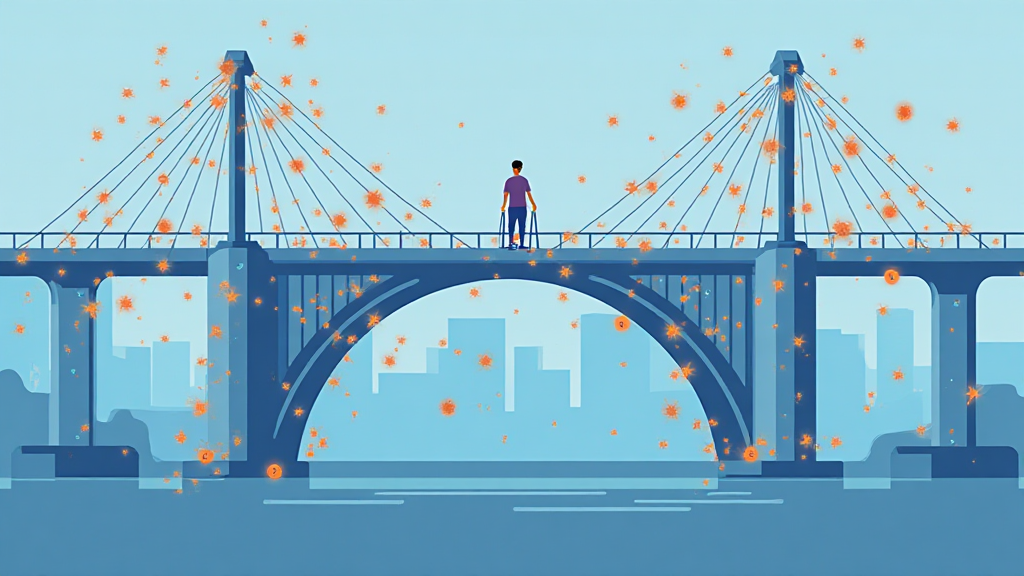
According to Chainalysis 2025 data, a staggering 73% of global cross-chain bridges have vulnerabilities. As the cryptocurrency market evolves, ensuring the security of these bridges is paramount to maintaining user trust and safeguarding assets. This guide delves into the current state of cross-chain technology and the crucial role that Vietnam Kubernetes hosting plays in enhancing security measures.
Understanding et=”_blank” href=”https://theguter.com/?p=8958″>et=”_blank” href=”https://theguter.com/?p=10083″>Cross-Chain Bridges
Imagine cross-chain bridges as currency exchange booths at an airport. Just as travelers convert their cash when crossing borders, cross-chain bridges alet=”_blank” href=”https://theguter.com/?p=1659″>low digital assets to fet=”_blank” href=”https://theguter.com/?p=1659″>low seamlessly between different blockchain networks. However, if these booths lack proper security protocols, they become easy targets for theft and fraud—similar to how cybercriminals exploit vulnerabilities in poorly secured bridges.
The Role of Kubernetes in et=”_blank” href=”https://theguter.com/?p=6760″>et=”_blank” href=”https://theguter.com/?p=6804″>et=”_blank” href=”https://theguter.com/?p=7600″>et=”_blank” href=”https://theguter.com/?p=7642″>et=”_blank” href=”https://theguter.com/?p=9026″>Enhancing Security
So, what does Kubernetes have to do with this? Think of Kubernetes as the traffic police for our airport. It orchestrates the movement of assets between blockchains and ensures everything runs smoothly. By leveraging Vietnam Kubernetes hosting, developers can deploy applications that enhance the security of cross-chain transactions, reducing the chances of exploits and breaches.
Key Security Protocols to Consider in 2025
In 2025, the landscape of DeFi regulations will be pivotal. With new regulations emerging, especially in key markets like Singapore, organizations will need to adapt their security measures accordingly. Look for protocols that prioritize user safety and compliance to navigate these changes effectively.
Comparing et=”_blank” href=”https://theguter.com/?p=6760″>et=”_blank” href=”https://theguter.com/?p=6804″>et=”_blank” href=”https://theguter.com/?p=7600″>et=”_blank” href=”https://theguter.com/?p=7642″>et=”_blank” href=”https://theguter.com/?p=9026″>Energy Consumption of PoS Mechanisms
Proof of Stake (PoS) mechanisms are becoming increasingly popular due to their energy efficiency compared to traditional Proof of Work systems. It’s like switching from a gas-guzzling car to a hybrid—better for the environment and your wallet. The environmental impact of blockchain technologies is a growing concern, and understanding this can help inform your investment decisions.
In conclusion, securing cross-chain bridges is essential for the continued growth and safety of the cryptocurrency ecosystem. Leverage Vietnam Kubernetes hosting to stay ahead of potential threats and navigate the complexities of DeFi regulations effectively. To explore more about this et=”_blank” href=”https://theguter.com/top/”>topic, download our comprehensive toolkit beet=”_blank” href=”https://theguter.com/?p=1659″>low.
Download the Security Toolkit Now!
Note: This article is for informational purposes only and does not constitute investment advice. Consult your local regulatory authority (such as MAS/Set=”_blank” href=”https://theguter.com/?p=6760″>et=”_blank” href=”https://theguter.com/?p=6804″>et=”_blank” href=”https://theguter.com/?p=7600″>et=”_blank” href=”https://theguter.com/?p=7642″>et=”_blank” href=”https://theguter.com/?p=9026″>EC) before making any investment decisions.
For more details on cross-chain security measures, check our white paper on ef=”https://hibt.com/cross-chain-security”>cross-chain security and discover tools like the Ledger Nano X, which can reduce the risk of private key exposure by up to 70%.